Beschreibung

Sophos heeft een nieuwe versie vrijgegeven van zijn XG Firewall met 18.0 als versienummer. Deze software wordt zowel op fysieke hardware als in een soft-appliance voor VMware, Hyper-V, Xen en KVM. A pre-authentication SQL injection vulnerability was recently discovered and fixed on Cyberoam operating system (CROS) devices. This type of vulnerability could allow SQL statements to be executed remotely, but only if the administration interface (HTTPS admin service) was exposed on the WAN zone. No other Sophos products were affected.
Verbesserungen
- Unterstützung für die neuen SD-RED 20 und SD-RED 60
- die kürzlich veröffentlichten Hotfixes HF051220.1 und HF052220.1 sind in diesem Release enthalten
- die XG Firewall Web Konsole gibt nun granularere Gründe an, warum Firmware-Uploads fehlschlagen
- Emails in Quarantäne können nur noch über das User Portal freigegeben werden
Über die nächsten Wochen wird das Release nach und nach automatisch auf den Geräten zur Installation zur Verfügung stehen. Sie können die Firmware auch manuell über das Licensing Portal herunterladen.
Bemerkungen
Das Upgrade auf v18 MR-1-Build396 ist möglich von folgenden Firmwareständen:
- SFOS 17.5 MR6
- SFOS 17.5 MR7
- SFOS 17.5 MR8
- SFOS 17.5 MR9
- SFOS 17.5 MR10
- SFOS 17.5 MR11
- SFOS 17.5 MR12
Das Update enthält die Bugfixes der Version v18 MR-1-Build367
Bugfixes
- NC-60108: [API Framework] Preauth SQLi in apiInterface OPCODE
- NC-59156: [CSC] Traffic not passing after upgrade to SF 18.0 MR1
- NC-59300: [Email] Blind pre-auth SQLi in spxd on port 8094
- NC-23160: [Firewall] LAN test failed in Port3 in SFLoader for 125/135 desktop model
- NC-59586: [Network Utils] Remove MD5 remnant
- NC-46109: [RED] No proper forwarding if bridging 3 or more RED s2s tunnels on an XG
- NC-50796: [RED] All RED site to site tunnel restart when configuring one RED interface
- NC-60162: [Reporting] Error 500 displayed for WebAdmin and UserPortal after HF4.1 applied on virtual XG
- NC-60171: Security, UI Framework] Admin to Superadmin privilege escalation
- NC-59427: [SFM-SCFM] SQLi in User Portal
- NC-59932: [UI Framework] Unable to login to user portal or admin using IE after HF4.1
- NC-30903: [Authentication] STAS configuration is editable via GUI on AUX machine
- NC-50703: [Authentication] Access server restarted with coredump using STAS and Chrome SSO
- NC-50716: [Authentication] Cannot import LDAP server via XMLAPI if client cert is 'None'
- NC-54689: [Authentication] Support download certificate for iOS 13 and above
- NC-55277: [Authentication] Service 'Chromebook SSO' is missing on Zone page
- NC-51660: [Backup-Restore] Restore failed using a backup of XG135 on SG230 appliance
- NC-55015: [Bridge] Wifi zone is not displayed while creating bridge
- NC-55356: [Bridge] TCP connection fails for VLAN on bridge with HA Active-Active when source_client IP address is odd
- NC-52616: [Certificates] Add support for uploading of CRLs in DER format
- NC-55739: [Certificates] EC certificate shows up as 'RSA' in SSLx CA cert dropdowns
- NC-55305: [CM (Zero Touch)] System don't restart on changing time zone while configured through ZeroTouch
- NC-55617: [CM (Zero Touch)] Getting wrong error message in log viewer after ZeroTouch process
- NC-55909: [Core Utils] Unable to see application object page on SFM
- NC-30452 : [CSC] Dynamic interface addresses not showing on Aux after failover
- NC-55386: [Dynamic Routing (PIM)] PIM-SM import fails with LAG as dependent entity
- NC-55625: [Dynamic Routing (PIM)] In HA with multicast interface, routes are not getting updated in the Aux routing table
- NC-55461: [Email] After adding/edit FQDN host with smarthost, it is not displayed on the list until refresh the page
- NC-58898: [Email] Potential RCE through heap overflow in awarrensmtp (CVE-2020-11503)
- NC-55635: [Firewall] Display filter for forwarded is not working properly on packet capture page
- NC-55657: [Firewall] HA backup restore fails when port name is different in backup and appliance
- NC-55884: [Firewall] IPS policy id and appfilter id not displaying in firewall allow log in logviewer
- NC-55943: [Firewall] Failed to resume existing connection after removal of heartbeat from firewall configuration
- NC-57084: [Firewall] Custom DMZ not listed in dedicated link HA configuration
- NC-44938: [Firmware Management, UX] Web UI does not surface reasons for firmware upload failure
- NC-55756: [Gateway Management] Gateway isn't deleted from SFM UI after deleting it from SFM
- NC-55552: [HA] WWAN interface showing in HA monitoring ports
- NC-55281: [Import-Export Framework] Full configuration import fails when using third party certificate for webadmin setting
- NC-55171: [Interface Management] VLAN Interface IP is not assigned via DHCP when gateway name uses some special characters
- NC-55442: [Interface Management] DNS name lookup showing incorrect message
- NC-55462: [Interface Management] Import fails on configuring Alias over VLAN
- NC-55659: [Interface Management] Invalid gateway IP and network IP configured using API for IPv6
- NC-56733: [Interface Management] Patch PPPd (CVE-2020-8597)
- NC-51776: [IPS Engine] Edit IPS custom rule protocol doesn't work after creation
- NC-51558: [IPsec] Add warning message before deleting xfrm ipsec tunnel
- NC-55309 : [Logging] Local acl rule not created through log viewer for IPv4 and IPv6
- NC-50413: [Logging Framework] Gateway up event log for PPPoE interface not always shown in logviewer
- NC-55346: [Logging Framework] Clear All for 'Content filtering' does not clear SSL/TLS filter option
- NC-56831: [Policy Routing] SIP traffic sometimes not working with SDWAN policy route
- NC-46009: [SecurityHeartbeat] Spontaneous reconnects of many endpoints
- NC-51562: [SecurityHeartbeat] Heartbeat service not started after HA failover
- NC-52225: [Synchronized App Control] SAC page loading issues as the list of apps increases
- NC-54078: [UI Framework] Internet Explorer UI issue on certain rules and policies pages
- NC-56821: [Up2Date Client] SSL VPN downloading with the 0KB
- NC-54007: [Web] File type block messages sometimes contain mimetype rather than file type
XG Firewall v18 MR1 is now rolling out globally, bringing new levels of visibility, protection, and performance to your firewall. When the notification for the latest firmware update appears in the console, we strongly encourage everyone to take advantage of the easy process to upgrade. It’s just a few clicks.
And if you haven’t already done so, now is the time to upgrade your XG Firewall to v18.
As there are many great new features in XG Firewall v18, our blog series over the coming weeks will be highlighting the most important new capabilities, such as the new Xstream Architecture, the new zero-day threat protection, Sophos Central Management and Reporting, and how you can get the most out of them.
Xstream Architecture
One of the flagship features in v18 is the new Xstream Architecture, which includes a streaming DPI engine and TLS 1.3 inspection for encrypted traffic.
How is this architecturally different to the legacy web proxy solution? Put simply, the new Xstream DPI engine is specifically designed to achieve optimal performance and connection-handling efficiency. It uses a single streaming engine that inspects traffic between a host on the network and an external server or service. This provides all the essential protection in a single pass:
- File and web malware scanning
- Intrusion Prevention (IPS) or attempts to exploit network vulnerabilities
- Application identification and control
By stream scanning files as they are downloaded from web servers, it can pass the content along to the end user while only holding the last portion of the file to complete the scan before either blocking the download or allowing the last packets to flow through. It does not need to hold the entire file while it’s being scanned.
Sophos Xg 18 Mr1
And it’s FAST! How fast? Many XG Firewall customers and partners have reported that the new DPI engine and TLS inspection are anywhere from two to three times faster than before.
Unlike the Xstream DPI engine, legacy protection in XG Firewall utilizes different engines for different jobs. There’s a web proxy for inspecting and filtering web content, an IPS engine, and an application control solution.
Sophos Xg 18 Mr1 Download
Rather than stream scanning as traffic flows through, the web proxy acts as a relay between the client and the external server. This has an advantage when packet header modifications need to be made to support features such as SafeSearch, YouTube restrictions, or Google domain restrictions as only the legacy web proxy can support these features. In all other cases, however, it just means it’s handling more connections and doing more work.
Making the most of the new Xstream DPI engine and TLS inspection

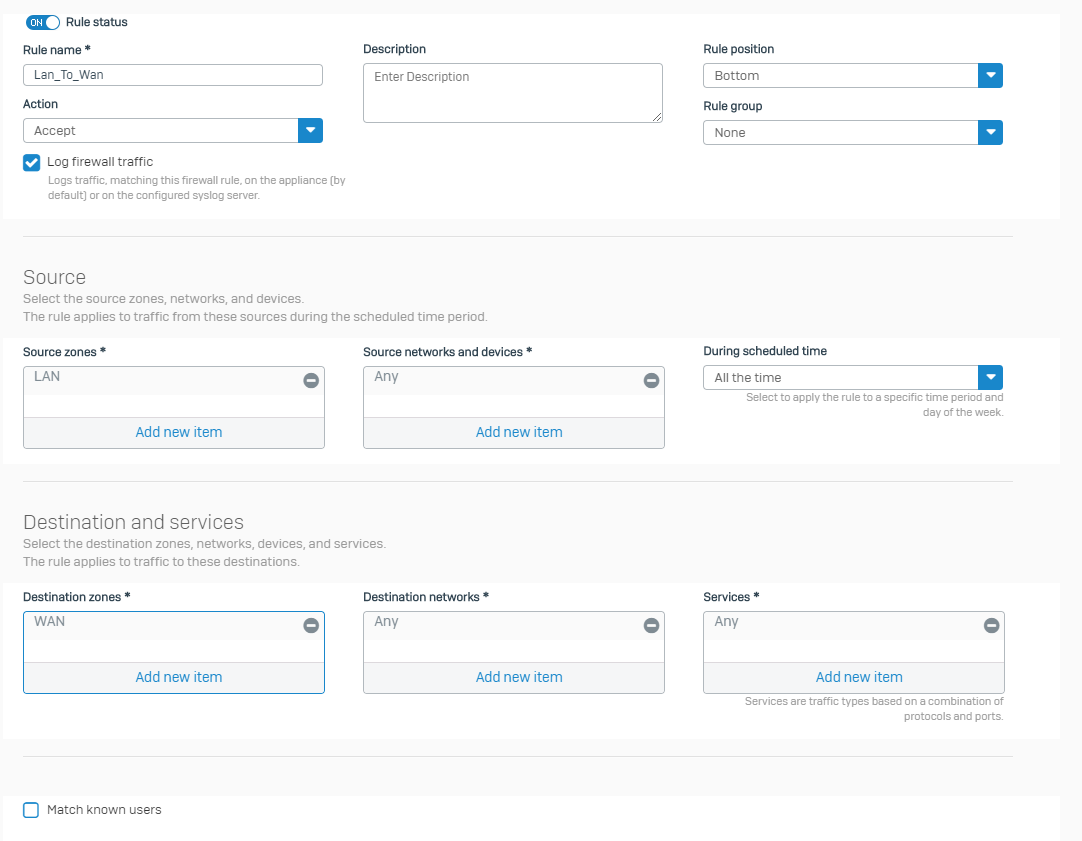
When you upgrade your XG Firewall to v18, all your existing firewall rules will be using the legacy web proxy by default to ensure seamless upgrade compatibility. If you don’t require features like SafeSearch, YouTube restrictions, or Google domain restrictions, you should switch these firewall rules to using the new Xstream DPI engine. It requires a change to a single setting:
This setting determines if you’re using the legacy web proxy (checked) or the new Xstream DPI engine (unchecked).
By switching many of your firewall rules over to the new Xstream DPI engine, you can see a tremendous performance benefit.
Taking advantage of the new TLS inspection engine with support for TLS 1.3 is also simple to configure. It essentially requires checking one box in your firewall to activate it and then creating a rule on the new SSL/TLS Inspection Rules tab as shown below.
As with any TLS inspection solution, you will also need to deploy the appliance CA certificate to hosts on your network that you wish to inspect. We recommend using the wizard built into the Microsoft Active Directory Group Policy Management tools to make this quick and easy.
Your TLS rules define which TLS traffic to decrypt and the associated decryption profile governs how to handle the decryption as well as protocol and cipher enforcement. The rules are structured and work identically to how firewall rules function in a top-down hierarchy.
We recommend you start gradually with TLS encryption, with a limited sub-estate of your network or a few test systems. This will allow you to build your expertise with the new TLS inspection solution and explore the new rules, logging, reporting, and error-handling options. Not all applications and servers fully and properly support TLS inspection, so watch the Control Center for errors and take advantage of the convenient built-in tools to exclude problematic sites or services.
Once you’re comfortable with the DPI engine and TLS inspection, we recommend applying it more broadly across your network. However, with encrypted traffic volumes now at over 80% of all internet traffic, keep in mind that TLS inspection is resource-intensive due to the nature of the decryption/encryption algorithms.
If your XG Firewall appliance is a few years old and already running at high load, it may be time for a hardware refresh or a new higher-performance model. Enabling TLS inspection on most of your internet traffic is now essential protection against the latest ransomware and threats as more and more hackers make use of TLS encryption to get onto networks and stay there undetected.
To learn more, the following resources are available to help you make the most of the new features in XG Firewall v18:
